RIP Windows XP and Office 2003!
Well, like it or not, Windows XP Home and Professional, as well as Microsoft Office 2003 support ends today, April 8, 2014.

Windows XP Home and Professional Support Ends today, April 8, 2014!
Windows XP support end: 10 steps to cut security risks – ZDNet
“While doing nothing is an option, we do not believe that most organisations — or their auditors — will find this level of risk acceptable,” vice president and Gartner fellow Neil MacDonald said in a report, Best practices for secure use of XP after support ends.
Between 20 percent and 25 percent of enterprise systems are still running XP, and one-third of organisations continue to use it on more than 10 percent of their machines, Gartner estimates.
For those still using the venerable OS after the end of routine Microsoft updates and security patches, MacDonald has come up with 10 best practices to minimise the risks.
Rest in Peace, Windows XP – PCMag SecurityWatch

Rest in Peace Windows XP 2001-2014 You will be missed! Image links to PCMag article.
This is the end. Your Windows XP computer will get its last update today. Oh, it’s not going to roll over and kick the bucket, but continuing to use it will be more and more dangerous, since any new vulnerabilities that arise won’t be patched. We checked in with a number of security experts to discuss just how risky life will be for those who continue to run XP.
It’s the end of the line for Windows XP – USAToday
The software — introduced in an era before texting, Facebook, Snapchat, the iPhone and iPad — has lingered thanks to the reluctance of many consumers and small businesses to change. Despite its age, XP is the No. 2 computer operating system, and many folks are in store for a rude wake-up call.
Microsoft on Tuesday ceases official support for XP. The company will no longer issue patches or system updates to protect against viruses and other malware. If you run into any snags at all, you won’t be able to call Microsoft for technical assistance.
Microsoft Ends Support for Windows XP – Mashable
“Microsoft has provided support for Windows XP for the past 12 years. But now the time has come for us, along with our hardware and software partners, to invest our resources toward supporting more recent technologies so that we can continue to deliver great new experiences,” wrote Microsoft in an announcement.
…
Launched on October 25, 2001, Windows XP is one of the most successful Microsoft products ever; its successor, Windows Vista, was quickly replaced with Windows 7, and it took as long as September 2012 for Windows 7 to overtake XP as the most popular desktop operating system.
Microsoft ends support for Windows XP and Office 2003 – TheNextWeb
If you’re wondering why April 8, 2014 is the date support for both of these products ends, it’s really quite simple. Microsoft releases regular patches on Patch Tuesday, the second Tuesday of every month.
Microsoft supports its products for many years, and depending on when service packs as well as successors are released, the company eventually announces, in advance, when it will cut off support. April 8 happens to be the last Patch Tuesday for both products, meaning if security holes are found after today’s date, they won’t be plugged.
Excellent point!
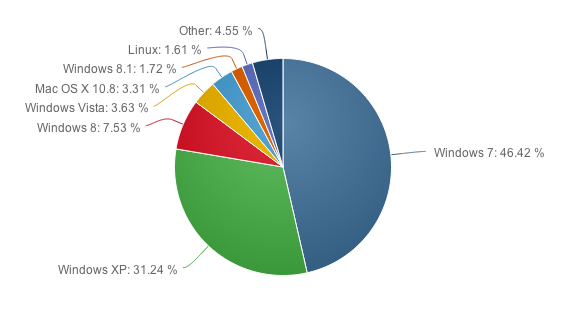
Netmarketshare.com for Operating Systems pulled today showed March 2014 tallies:

Networkmarketshare, as of March 2014, pulled today, still shows Windows XP as 27.69% of the MarketShare. Link goes to metmarketshare.com
I personally still find it unbelievable that Microsoft, or any company really, would retire/pull support an OS that still garners nearly 30% of Windows users around the world.
Of course if you are an Enterprise company that can afford $200 PER PC for the first year, and increasing amounts each year THEREAFTER for Windows XP updates (security updates only by the way)…
Windows XP support will be available after April 8—just not for you – PCMag
Meet Microsoft’s Custom Support for Windows XP, described as a last-ditch effort for big businesses to quite literally buy some more time to migrate from Windows XP to a more modern operating system. The U.K. paid 5.548 million pounds to Microsoft for an additional year of support to maintain critical and important security updates for Windows XP, Office 2003, and Exchange 2003. Otherwise, Microsoft plans to end support for Windows XP by April 8.
Microsoft has been warning about the demise of Windows XP support since September, 2007, and Custom Support will extract a heavy toll from businesses that were too slow to act: up to $5 million per year (according to a report from Gartner), negotiated on a custom, per-company basis. Last year, Gartner issued a report claiming that the prices could go as high as $200 per PC, per year. The firm called such prices “punitive”.
…
Should consumers get the same break?
To date, Microsoft has given no indication that it will extend consumer support for Windows XP after the April 8 deadline, even though it has extended anti-malware support through July, 2015. After that date, any and all vulnerabilities found for Windows XP will live on forever, even though there are some avenues to keep your PC safe and protected after the deadline expires.
BTW: Apple‘s Mac OS X Mavericks holds 3.75% of the market (putting it between Windows 8.1 and Vista), however, if you include all Mac OS X operating systems listed: Mac OS X 10.6 1.29% (support ended), Mac OS X 10.8 1.18%, Mac OS X 10.7 1.05% Mac OS X 10.5 .24% (support ended), Mac OX X 10.4 0.06% (supported ended), and Mac OS X no version reported 0.01%, then the total is 7.58% of the operating system total market share (which puts it on the low end between Windows XP and Windows 8).
But, that does mean that only 1.59% of all Mac OS X users are running expired versions with no support.
Compare that with 27.69% of Windows users running Windows XP.
NOTE: That doesn’t count the expired/no support users running Windows NT at 0.15%, Windows 2000 at 0.03%. Apparently Windows 98 users have finally fallen off at 0.00%.
Windows XP end of support: why it concerns you – OnWindows.com
Reto Haeni explores the risks of running Windows XP after its end of service and the benefits of migrating to newer operating systems
This article was first published in the Spring 2014 issue of Touch
…
Designed in a different era
Computers running Windows XP routinely experience a significantly higher malware infection rate than computers running any other supported version of Windows. Much of the elevated infection rate on Windows XP can be attributed to the fact that some of the key built-in security features included with more recent versions of Windows are not present in Windows XP. Windows XP, designed in a different era, simply can’t mitigate threats as effectively as newer operating systems, like Windows 7 and Windows 8. As the threat landscape has evolved over the past twelve years since the release of Windows XP, so has software security.
It’s time folks! If you haven’t done it yet, and if you are still running Windows XP on the Internet, it is high time to correct this by upgrading to a modern OS that is still supported, or disconnect from the Internet.
Please, unless you are a technical person who truly understands the risks and has taken steps to mitigate the overwhelming risks, then please be responsible and disconnect your Windows XP computer now!
Or move to new computer running a current version of Windows, or a Mac from Apple, or the Open Source ‘UNIX like’ Linux operating system and run Windows XP programs with Crossover as suggested here, or you could use Windows XP offline, and use a Linux LiveCD for Internet surfing and email, etc as suggested here and not mess up your offline Windows XP system. No matter how you do it, PULL THE PLUG on Windows XP – Disconnect the Ethernet or Wireless connection to the Internet! Just as soon as you get any April 8th Windows Updates on Patch Tuesday.
Unless you know what you are doing, you will be playing Russian Roulette with your Windows XP computer if you allow it to be online once Microsoft ends support after April 8, 2014. And that has been only Life Line extended support since 2009.

Microsoft Office 2003 support ends today, April 8, 2014!
We also mentioned Microsoft Office 2003. Oh, yes, Microsoft Office 2003 has also expired today. No more security updates will be provided for Office 2003 either, just like Windows XP.
If you are still using Office 2003, it’s high time to remove it and move to a current version of Microsoft Office, or move to one of the Open Source alternatives such as; Apache Foundation‘s OpenOffice.org or Document Foundation‘s LibreOffice, or move to using online versions of MS Office software like MS Office Web Apps or move over to Google’s online document handling programs; Google Docs.










You must be logged in to post a comment.